![]() This functionality is available for PRO version.
This functionality is available for PRO version.
WordPress is the most popular CMS system, being used on over 37% of total sites, which is an astonishing achievement. There’s no doubt, WordPress is a unique framework, is a good and flexible core skeleton, a nice and easy to follow administrator dashboard interface. Not at least it provides a large base of free plugins and themes which conclude to incredible extensibility at the distance of a few mouse clicks.
But All that popularity comes with a huge price, hackers are very active in finding security breaches in WordPress sites, as opening an exploit reveal the vulnerability for all other sites using similar applications.
What is a Firewall?
A Firewall is a security piece of software that adds a layer of protection to your site. A firewall works as a rules-based filter for all incoming traffic to a website, it ensures only the secure traffic is reaching the server, all malicious attempts will be blocked and logged.
Why use a Firewall?
A Firewall works as Proactive ratter reactive security solution, so it helps to protect a website before the malicious and malware actually reach it. This is a huge improvement for security, as preventing any harm and damages to a site, spare the administrators of incalculable losses which the malware can do.
What the WP Hide Firewall can do?
The Firewall core is based on the well-known 7G Firewall solution used on a large number of servers. Is a lightweight code, a well-optimized set of rewrite rules, server-level protection against a wide type of malicious request, bad bots, automated attacks, spam, and other types.
Some of the firewall features are:
- Security via simplicity
- Extensive firewall protection
- Fine-tuned to minimize false positives
- Lightweight (only 12KB!), modular, flexible and fast
- Completely plug-&-play with no configuration required
- Improves security, reduces server load, and conserves resources
- Git/SVN friendly (does not block svn/git files et al)
- Better bad bot detection
Types of attacks and threats the firewall can stop:
- Directory Traversal
- HTTP Response Splitting
- (XSS) Cross-Site Scripting
- Cache Poisoning
- Dual-Header Exploits
- SQL/PHP/Code Injection
- File Injection/Inclusion
- Null Byte Injection
- Plugins exploits such as revslider, timthumb, fckeditor
- Exploits such as c99shell, phpshell, remoteview, site copier
How to activate the Firewall?
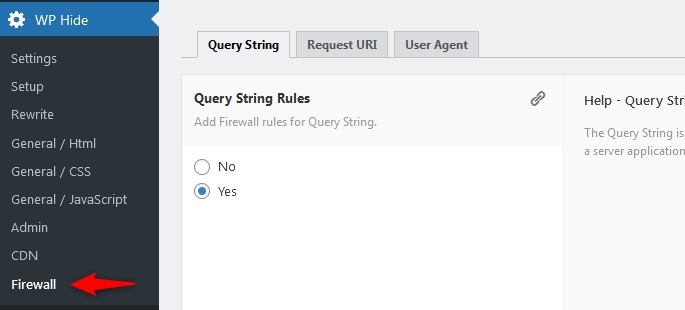
The feature works as an out-of-the-box solution, through the plugin Firewall interface the options need to be activated.
There is 3 types of firewall rules:
- Query String Rules
- Request URI Rules
- User Agent Rules
The Query String Firewall module, scans the portion of a URL where data is passed to a server application and/or back-end database.
The Request URI Rules, known as Uniform Resource Identifier, identify the resource upon which to apply the filters.
The User Agent rules, helps to block known malware boots and hack scanners.
The plugin interface includes a separate menu item for the firewall which can be used to control the active modules: